Learn about dynamic application security testing (DAST). Understand how DAST works, its pros and cons, and its importance in AppSec.
Learn about dynamic application security testing (DAST). Understand how DAST works, its pros and cons, and its importance in AppSec.

Discover the top 11 web vulnerability scanners and learn why they are essential for protecting your web applications from hackers.

Learn about Docker image security scanning and its limitations. Understand how scanning works, why it’s important, and more.
Learn all about Mend’s 2021 Open Source Security Vulnerabilities Report, including new challenges, common vulnerabilities, and more.

Discover the best coding Easter eggs in this blog post by Mend.io. From Google search to Mozilla Firefox, uncover hidden surprises in tech.
Forrester’s State Of Application Security Report for 2021 highlights key trends and recommendations for effective AppSec strategies in a rapidly evolving digital world.

Discover why open source software is often more secure than commercial software, and the benefits of using open source components.

Stay informed about the most critical Linux kernel vulnerabilities. Our guide covers the top 10 CVEs and offers tips for maintaining security.

Discover how Mend practices what they preach by using their own software to develop secure products.
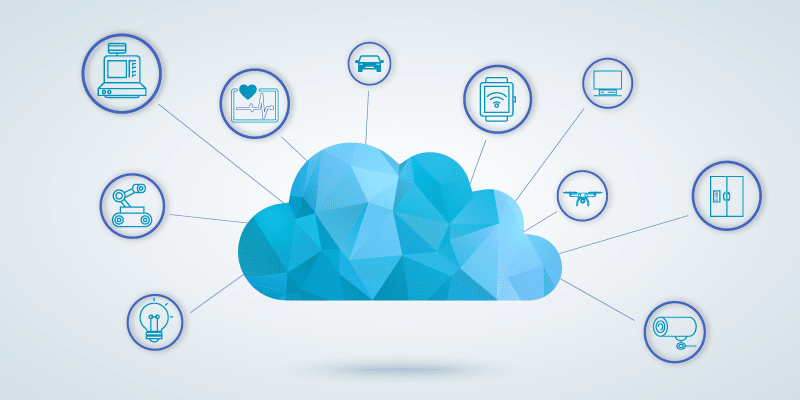
Discover the importance of securing your IoT devices with tips on network and device security, application layer protection.
Learn about the differences between open source and proprietary software security in this comprehensive guide.
Learn how to manage alert fatigue in application security. Discover strategies for prioritizing and remediating security alerts.

Learn how to set up an effective vulnerability management policy to minimize security risk and stay compliant with regulations.

Explore the world of RASP – Runtime Application Self-Protection in this informative blog post. Learn why developers need it.

Learn about serverless security in the cloud ecosystem, including best practices like staying up to date, least privilege, and more.

Discover the top 3 open source risks: security vulnerabilities, licensing compliance, and quality issues. Learn how to mitigate these risks.