Dynamic testing
Test applications while they’re running, simulating real-world attacks to identify security vulnerabilities.
Challenges
Complex, ever-growing risk
AppSec teams and developers alike are inundated with security findings. Understanding and securing their rapidly evolving application attack surface, and doing so at scale, is more challenging than ever.
Real threats vs. Theoretical risk
Even with comprehensive testing early in development, it’s possible for vulnerabilities to surface during execution. False positives make it challenging to cut through the noise to understand what real threats exist.
Manual bottleneck
Gaining visibility into risks that emerge while your apps are running is time-consuming without the right tools, and manual testing can’t scale. Without automation and integrations, security becomes a bottleneck to development velocity.
Sprawl and lack of visibility
The proliferation of cloud-native assets and microservices is expanding your attack surface faster than you can manage. Lack of visibility across your true attack surface leaves unknown assets and APIs vulnerable.
Opportunities
Secure what’s real
Test for security risks as your apps are running – prioritizing reachable, exploitable risks and gaining comprehensive visibility from code to cloud.
Prioritize with precision
Mute the noise with reachability and exploitability insights that ensure you’re prioritizing real risk. Dynamic testing insights from DAST, API, and Container security scans help you focus and fix faster.
Automate, integrate, scale
Automate DAST, API, and Container security scans across multiple points in your development lifecycle. Seamlessly integrate across development pipelines and workflows, to streamline remediation and developer feedback.
Discover and protect
Gain complete visibility into all your applications and APIs, including those that are lost, undocumented, or unauthorized, so your known attack surface and security coverage remains up to date even as environments change.
The solution
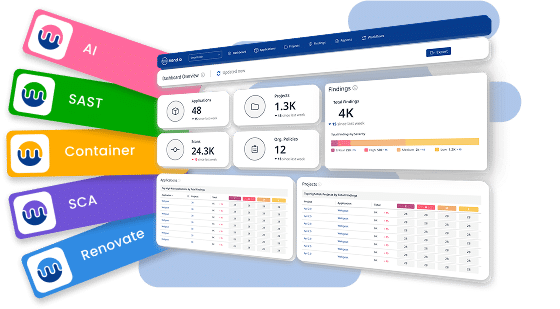
Mend AppSec
Application security coverage from code to runtime
Pair the platform with DAST and API Security from Invicti to extend your visibility and security coverage into runtime.
Discover Mend AppSec